2016 KCSE Computer Studies Paper 1 Past Paper
Questions and Answers
No. 1.(a) State the meaning of the term disk defragmentation as used in computers. (1 mark)
❖ The process of rewriting parts of a file to contiguous sectors on a disk
(b)State the purpose of disk defragmentation. (1 mark)
❖ to increase the speed of access and retrieval of files. + to increase space on the disk space
No.2. Identify the appropriate computer output device suitable for each of the following tasks: (a) generating receipts where carbon copies are required; (1 mark)
❖ Carboncopies – impact printers e.g. dot matrix.
(b)an architectural drawing where precision is required; (1 mark)
❖ Architectural design – plotter
(c) producing document output for a visually impaired person. (1 mark)
❖ Visual impairment – speakers/ brailles
No.3.Pesa Tele Company has offices in Nairobi and Kampala connected in a network. The management is convinced that someone is illegally gaining access to the data in their computers. State three ways in which the company can overcome this problem. (3 marks)
❖ Encryption.
❖ Firewalls.
❖ User profiles/ passwords/user.
❖ Limit the number of log-in attempts.
❖ Audit trail/ tracking.
❖ Physical protection of computers.
No.4.Explain two ways in which the use of Internet could make reporting of corruption easier.(4 marks)
– Interactiveness: ❖ the internet based technology enables real-time dialogue hence instantaneous reporting of cases; Outreach:
❖ the technology allows the coverage of wide areas/ can be reported from anywhere; Social mobilisation:
❖ It is easy to use technology to create a network with people or organisations with similar concerns; – Anonymity:
❖ With use of the technology, it has become easy to report corruption cases without being known; Security: The message sent reaches the destination with less risk of being intruded
No.5. State two ways in which software errors can be prevented in program development. (2 marks)
❖ Use of anti-virus software.
❖ Update system frequently.
❖ Purchase software from authentic sources.
❖ Test the software before implementation.
❖ Test syntax/ logic.
❖ Proper training.
❖ Proper enactment of laws.
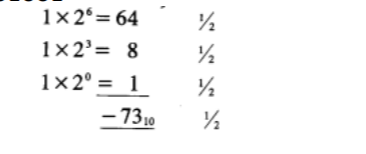
No.6.Convert each of the following binary numbers to decimal equivalent given that the left most digit is a sign bit:
(a) 00101101
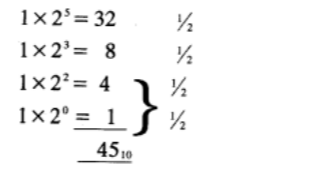
(b) 11001001
No.7.State the functions of each of the following keys on the computer keyboard: (2 marks)
(a) backspace;
❖ moves the display cursor one position backwards, deletes the character at that position, and shifts back the text after that position by one position
(b)insert (ins)
❖ When insert is selected, keys add characters to the screen at the cursor (insertion point) without deleting those already there. When typeover is selected the new characters type over the old, deleting them as they go
No.8. An organisation intends to replace an existing system by carrying out the process in stages. (a) Name this implementation strategy; (1 mark)
❖ The implementation strategy is: – phased change-over/modular
(b)Give two reasons why the organisation is opting to use the implementation strategy in (a) above. (2 marks)
❖ It gives employees opportunity to learn
❖ Organization can revert to old system in case of failure.
❖ Reduces resistance by employees.
(c) A manager wishes to replace the current manual system with a computerised one. Describe three main areas that must be evaluated to justify the replacement. (6 marks)
– Technical feasibility:
❖ Does’ the current technology (hardware & software) allow.
– – Economic feasibility:
❖ Are funds available? Social feasibility:
❖ How will the new system impact on the organization/ society?
No.9.Headache, back and neck pain may result from the use of computers. State how each of them can be minimised. (2 marks)
❖ Headache
❖ Use of filters/ antiglare.
❖ Proper lighting.
❖ Regular break.
❖ Back as Neck Pain
❖ Proper/ correct furniture for the computer.
❖ Correct position of the screen.
❖ Correct sitting posture.
❖ Taking a break.
No.10. Students of a school intend to elect their school captain by secret ballot. State three ways in which computers can be used to improve the election process. (3.marks)
❖ Registering voters/ (faster);
❖ Voter identification (accurate);
❖ Actual voting;
❖ Tallying process (speedy).
No.11. Explain why an intranet is a more secure way to share files within an organisation compared to the Internet. (2 marks)
❖ Intranet involves interconnection of computers within an organisation, in intranet it’s easier to monitor the access and sharing of files since the users working in the organisation can be assigned accounts and passwords which will enable them access the files they are authorised to access unlike the internet where many people can access whatever is stored in the organisation website.
No.12. List two career opportunities directly associated with computer networking. (2 marks)
❖ Network administrators + Network engineers
❖ Network technicians
No.13. Distinguish between a formula and a function as used in spreadsheets. (2 marks)
❖ A formula is a mathematical expression that creates a relationship between cells to return a new value while a function is an inbuilt predefined formula that the user can quickly use instead of having to create a new one every time they want to do a calculation
No.14. The C directory of a computer has folders named Form 1, Form 2, Form 3 and Form 4.
Each class has students’ folders named according to their admission number. The students created their own folder for subjects they are studying based on the table shown below:
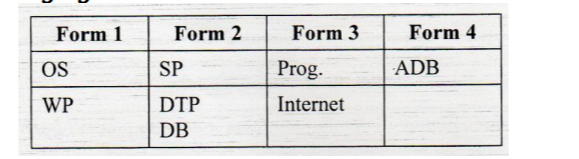
(a) A form four student intends to create a folder named proj to store project documents. State the path for the project folder. (1 mark)
❖ C:\FORM4\STUDNO\ADB\PROJECT
(b) Suggest how the student can ensure that: (i) work is not lost in case the hard disk fails; (1 mark)
❖ Keep backup copies of the project on offline secondary storage media.
(ii) the project is not copied by other students. (1 mark)
❖ Use passwords for opening and modifying the project
No.15.A water company sends out clerks to read meters. The data collected by the clerks is then fed into the computer and then all bills are printed at the same time.
(a)State two advantages of this approach; (2 marks)
❖ Shifts time of processing to when computers are less busy.
❖ No user input required hence no idle computer time as it awaits input.
❖ Input is done once (batch).
❖ Can enable use of hired equipment hence cost effective.
(b) Name this type of data processing.(1 mark)
❖ Batch processing.
❖ Electronic
No.16. Figure 1 shows a flowchart. Use it to answer the questions that follow.
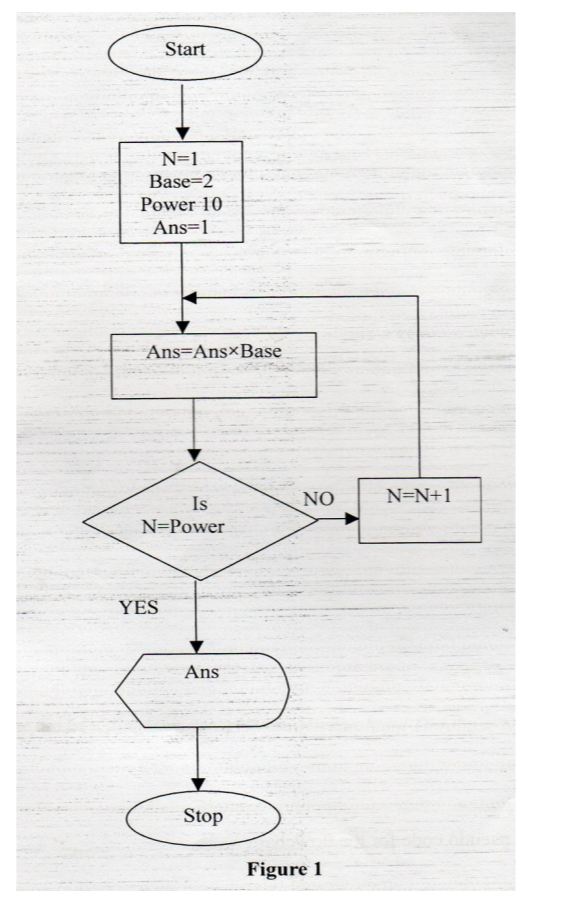
(a) Interpret the flowchart. (9 mark
(b) Write a pseudo code for the flowchart. (6 marks)
No.17.(a)With the aid of a diagram, describe the Hierarchical Database Model. (4 marks) evel 1 data item

❖ Data items are arranged in a tree like format.
❖ Access is through a single path and all from one single item called the root component
(b) List three factors that should be considered when developing a database application and give reasons why each should be considered. (6 marks)
Factors
❖ Complexity of data/ user needs/ user friendliness
❖ Security and integrity
❖ Complexity of DBMS
❖ Volume of data/ size ❖ Software compatibility with existing DBMS ❖ Cost of the data base
Reasons
❖ Complexity of data – Complex data requires complex DBMS.
❖ Security and integrity – Data which is intended to be secured in terms of access, can be handled by complex DBMS which provides for such requirements.
❖ Complexity of DBMS – Complex DBMS do require complex skills, hence more training. It is therefore costly to run/ use such system.
❖ Volume of data – Voluminous data require to be ran on stable application. They also take up extra computer system resources.
❖ Software compatibility – enables pre-existing databases to be exported to the new one.
(c) (i) Name three types of validation checks during data entry in data processing.(3 marks)
❖ Field type/ data type
❖ Field size
❖ Format
❖ Reasonableness
❖ Range constraint
❖ Presence check
(ii) Differentiate between primary key and index key as used in databases. (2 mark)
❖ Any index key is a database feature used to speed up search and sort operations in a table; whereas
❖ A primary key is a field that enforces uniqueness in a table so that one record is not entered twice or a primary key is a field that uniquely identifies each record.
No.18.(a) Explain two health issues that could arise from the use of unsuitable computer desk. (4 marks)
❖ It could lead to back problems if the desk is of an unrealistic height.
❖ If it does not provide good positioning of the monitor, it could result in eye strain.
❖ Wrist problems will arise if the keyboard and mouse seating positions are bad.
❖ Injury as a result of falling computer components due to weak computer desks/ small size.
No.18 (b i)Describe two ways in which a positive number and a negative number can be represented in a computer (2 marks)
❖ In binary one bit usually the most significant or leading bit is used to indicate either positive or negative,and store the unsigned binary representation of the magnitude in the remaining bits.
❖ Signed magnitude.
❖ Using the twos complement.
❖ Using the ones complement.
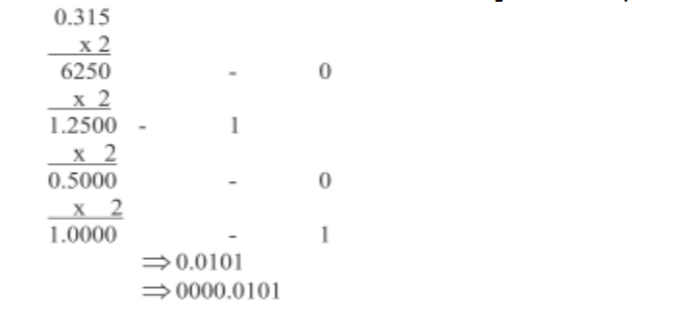
(ii) A particular computer stores numbers in a single 8-bit word. Determine how the number 0.3125 10 would be represented. (3 marks)
No.19.(a) Figure 2 shows a block diagram of a computer system and its peripheral devices. Use it and answer the questions that follow.
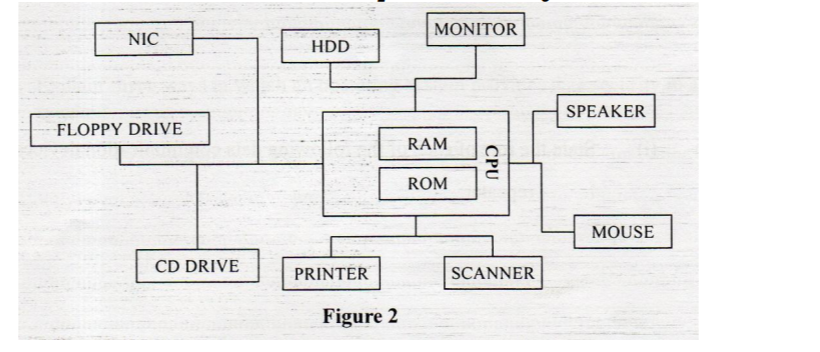
(i)Name two devices that may be used for storing data for a long duration. (2 marks)
❖ 2GB HDD
❖ 32 MB Rom
(ii) Name three peripheral devices that are used for input.(3 marks)
❖ Mouse
❖ Scanner
❖ CD drive
(iii)Name two other devices that a Computer Aided Design (CAD) user might wish to add to the set up above in order to perform his tasks effectively. (2 marks)
❖ Digitizer
❖ Keyboard
❖ USB port
19 (b) A customer wishes to purchase a computer system. The customer can buy word processor, spreadsheet, database, and a drawing package separately or as an integrated package. State three reasons why the customer would prefer an integrated package to separate packages(3mks)
❖ The software provides easy movement of data among the separate applications,
❖ A common group of commands is used for all the applications in the software package,
❖ Provides easy switching between functions without having to go back to the operating system and ability to share data between functions.
No.20.(a)Explain three ways in which an operating system provides data security in a computer system (6 marks)
– Access control: ❖ Deals with the problem of verifying / authenticating the identity of a user before permitting access to the request resource (e.g. use of passwords, user account);
– Encryption ❖ Transforming data into an unreadable format so that they are safely transmitted;
– Firewalls ❖ Filters out unwanted data and programs/ criminas/ hackers/ malicoius persons;
– Log files ❖ A means by which transactions in a computer system can be recorded thereby detering potential infiltrators; Alerts ❖ Alerting a user when he/she is about to delete a file/ folder.
20.(b)State two instances where observation is not a viable method of gathering data during system analysis stage. (2 marks)
❖ When the analyst wants to collect confidential information,
❖ When there is a large group of people involved in the system,
❖ Where the people you want to gather information from are vastly dispersed
(c) (i) State the role of each of the following data communication devices: I. repeater (1 mark)
❖ A device used to re-construct data signal during data transmission to its original strength/ amply boost/ regenerate.
II. router. (1 mark)
❖ It is a device used to facilitate movement of data or packets between two or more LANS of different configuration (expansion of networks).
❖ Delivers a packet/ data directly to destination computers.
❖ Interconnects different networks/ provides network services.
(ii) The figure below shows a network based on the bus topology.
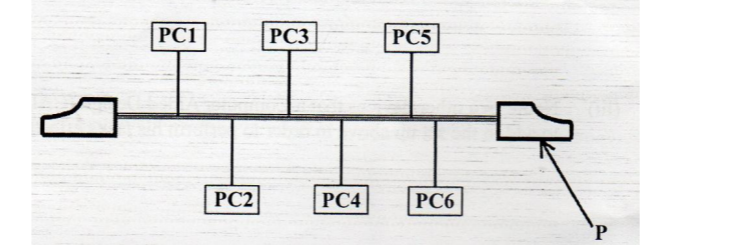
I. Identify the component labelled P.
❖ The component P is the terminator. II. State the function of the component labelled P.
❖ Terminator in a backbone is used to prevent data signal from bouncing back/ absorb signals.

