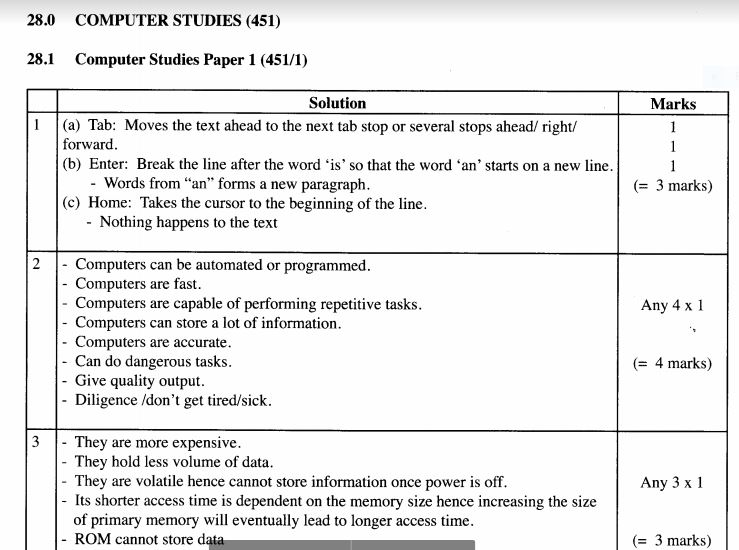
2011 KCSE Computer Studies Past Paper
4.11.1 Computer Studies Paper 1 (451/1)
SECTION A (40 marks)
Answer all the questions in this section in the spaces provided.
1 The text in the box below was composed using a wordprocessor. The current cursor position is between the Words “is” and “an”.
Describe what happens to the text in the box above when each of the following keyboard keys are pressed. .
(3 marks)
(a) tab
(b) enter
(c) home
2 State four characteristics which make computers better than human beings. (4 marks) 3 Give three reasons why primary storage devices are not used for secondary storage. (3 marks)
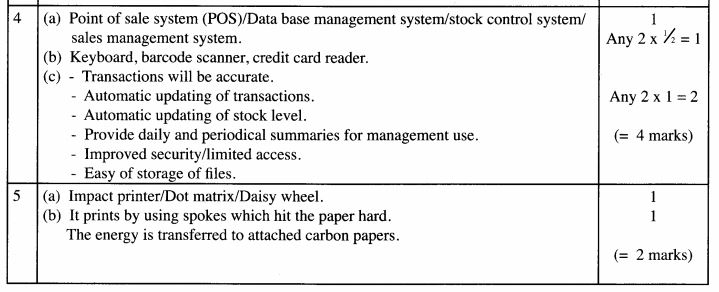
4 Asha has a hardware shop and lately. she is finding the task of managing daily sales in the shop overwhelming.
(a) State a retail system that she should acquire. (1 mark) (b) State two input devices that are used in retail systems. (1 mark)
(e) Apart from enhancing the speed of operation, state two other benefits that Asha will gain from using such a system. (2 marks)
5 The accounts department of a secondary school is using a system that generates invoices that are printed in triplicate using carbon papers.
(a) Name one type of printer suitable for this task. (1 mark)
(b) Give a reason for your answer in (a) above (1 marks)
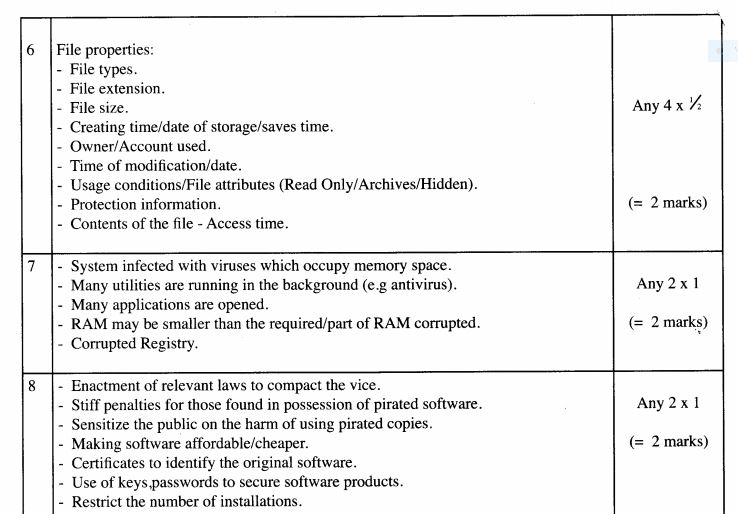
6 A secretary saved a document in a computer. After some time, she could not remember the name and the location of the file. State four file details that are assigned a file by the operating system which can assist in tracing the file. (2 marks)
7 A student tried opening an application program on a computer that was functioning well. The program did not load and the operating system reported that the memory was insufficient. Give two causes of such response. (2 marks)
8 State two measures that can be put in place to control piracy of software. (2 marks)
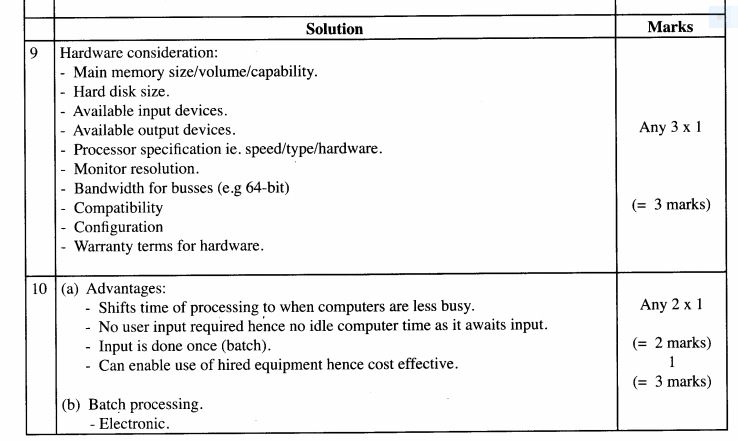
9 Identify three hardware considerations to be made before installing an operating system. (3 marks)
10 A water company sends out clerks to read water meters. The data collected by the clerks is then fed into the computer and then all the bills are printed at the same time.
(a) State two advantages of this approach. (2 marks)
(b) Name this type of data processing. (1 mark)
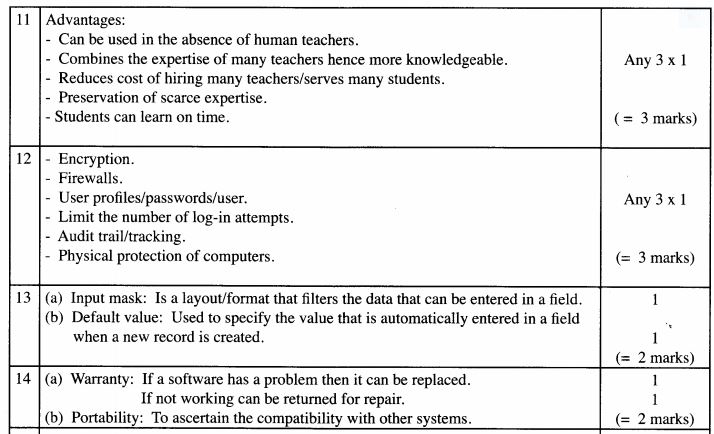
11 A school has acquired a system that imitates human teachers. Students can learn by getting answers from the system which they would normally get from the teacher. Give three advantages of this system. (3 marks)
12 Pesa Mingi company has ofiices in Nairobi and Kampala connected in a network. The management is convinced that someone is illegally gaining access to the data in their computers. State three ways in which the company can overcome this problem. (3 marks)
13 State the purpose of each of the following in database design.
(a) input mask (1 mark)
(b) default value (1 mark)
14 State the importance of considering the following factors when acquiring a software.
(a) warranty; (1 mark)
(b) portability. (1 mark)
15 State two application areas of real time systems. (2 marks)
SECTION B (60 marks)
Answer question 16 and any other three questions from this section in the spaces provided.
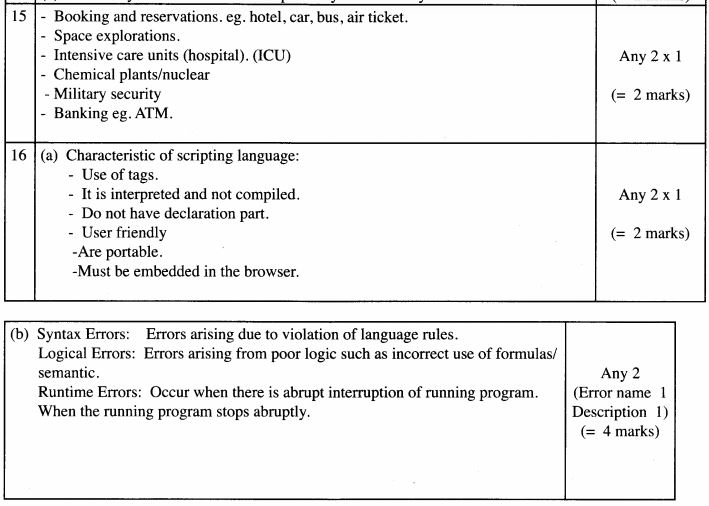
16 (a) Give two characteristics of scripting languages. (2 marks)
(b) Describe two types of errors that may be detected during program testing. (4 marks)
(c) A company’s workers travel to work either by public or by private means. All workers are paid a travel allowance of Ksh. 200, but those using private means are paid an additional Ksh. 100.
(i) Write a pseudo code to determine a worker’s travel allowance. (3 marks)
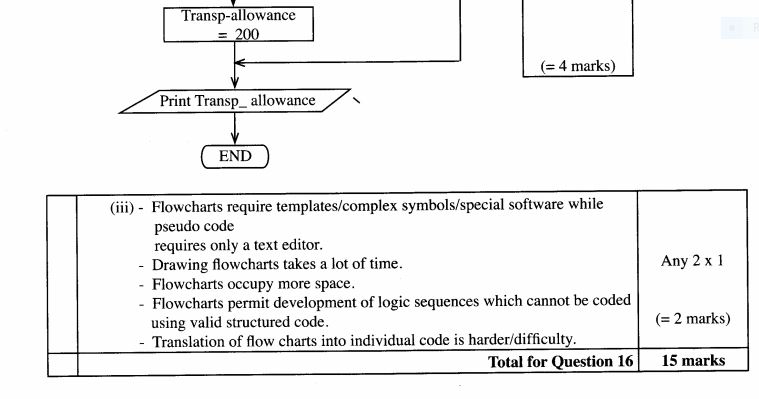
(ii) Draw a flowchart to determine a worker’s travel allowance. (4 marks)
(iii) Other than occupying large space, state two disadvantages of using a flowchart instead of a pseudo code. (2 marks)
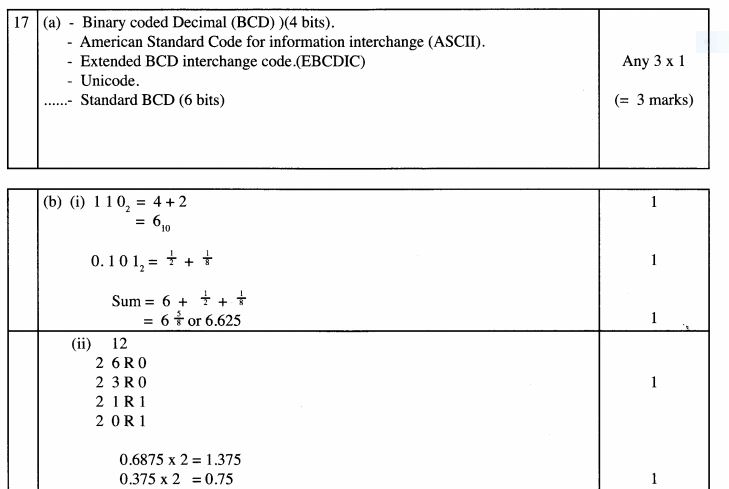
17 (a) State three standard data coding schemes used in computing and electronic systems. (3 marks)
(b) Convert each of the following numbers:
(i) 110.1012 to decimal; (3 marks)
(ii) 12.687510 to binary; (4 marks)
(c) Subtract 110.012 from 11OO1.Ol0l2. (2 marks)
(d) Using twos complement, perfonn the following binary arithmetic leaving the answer in binary notation. 110l2-1001012 (3 marks)
18 (a) What is meant by each of the following terms as used in table creation?
(i) cell margin; (1 mark)
(ii) nested table. (1 mark)
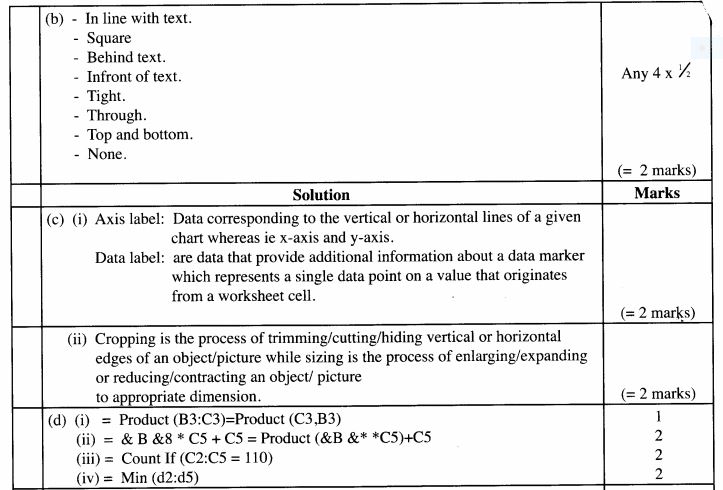
(b) State four types of text wrap that can be applied to a graphic. (2 marks)
(c) Distinguish between each of the following:
(i) axis labels and data labels; (2 marks)
(ii) cropping and sizing. (2 marks)
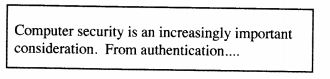
(d) Figure 1 shows a section of a worksheet containing information on household items. Use it to answer the questions that follow.
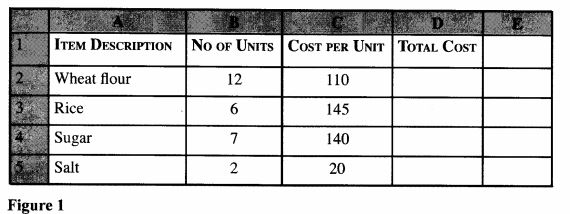
Figure 1
(i) Write a formula to calculate the total cost of rice. (1 mark)
(ii) The prices of all items increased by 10% and the value 10% is placed in cell B8. Using cell addresses with absolute referencing only, write a formula to calculate the new unit price of salt. (2 marks)
(iii) Write a function to display the number of cells in which the cost per unit is equal to 110. (2 marks)
(iv) Write a function to display the least total cost for all items. (2 marks)
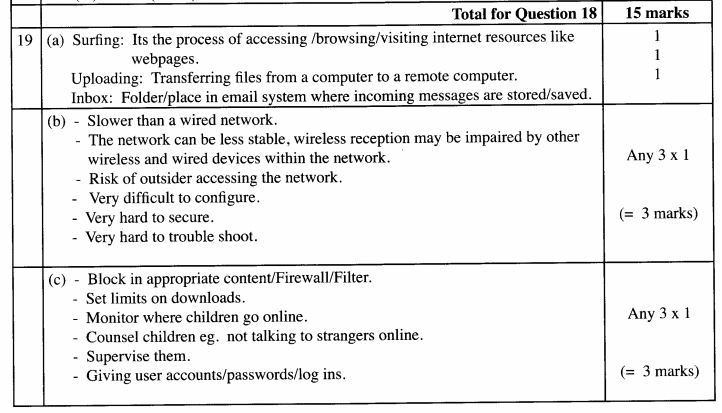
19 (a) What is meant by each of the following terms as used in the inter-net?
(i) surf; (1 mark)
(ii) uploading; (1 mark)
(iii) inbox. (1 mark)
(b) A school has set up its network using wireless technology to link computers. State three problems that the school is likely to experience when using this technology. (3 marks)
(c) List three ways by which parents can protect their children from accessing inappropriate content from the internet. (3 marks)
(d) Explain three problems associated with using e-mail technology for communication. (6 marks)
20 (a) Explain three reasons why an organization may need to change to a new computerized system. (6 marks)
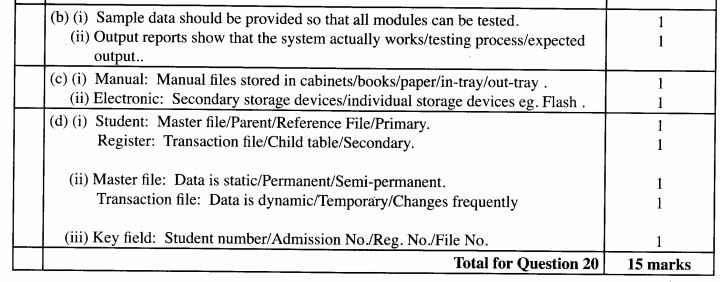
(b) State why each of the following is important in system documentation.
(i) sample data; (1 mark)
(ii) output reports. (1 mark)
(c) Name the tools used for data storage in each of the following methods of data processing.
(i) manual; (1 mark)
(ii) electronic. (1 mark)
(d) A teacher manages students‘ records by storing daily attendance information in a file called register and students’ personal records such as year of birth and home address in a file called students.
(i) Identify the types of computer files named above. (2 marks)
(ii) Give a characteristic of data held in each file. (2 marks)
(iii) Name the field that should be used to link the two files. (1 mark)
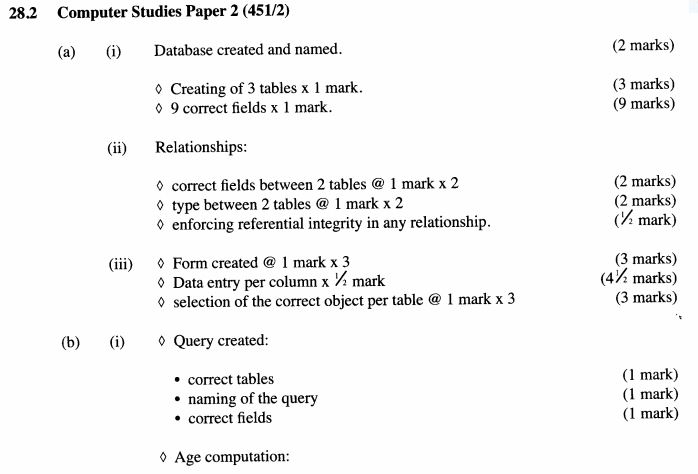
4.11.2 Computer Studies Paper 2 (451/2)
1 The data in the tables below was extracted from a survey data on employment.
Table 1: EMPLOYEE TABLE
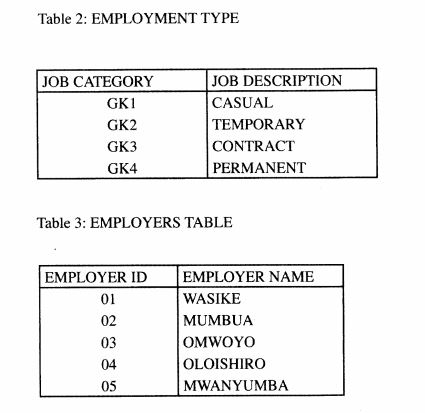
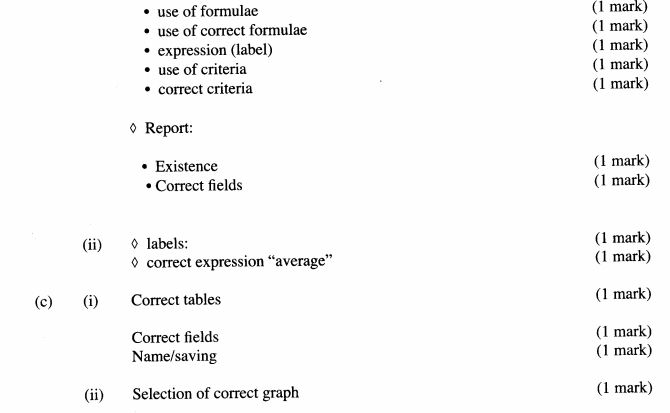
(a) (i) Create a database named “EMPLOYMENT” to store the data above. (14 marks)
(ii) Create relationships between the tables. (4% marks)
(iii) Use forms to enter data into the tables. (10 marks)
(b) (i) Generate a report to display the Name, year of birth, age and employers name for the employees who will be over 30 years old by the year 2012. (10 marks)
(ii) Compute the mean age of employees on the report you created in b(i) above. (2 marks)
(c) (i) Create a query to display the employees and their job description. Save the query as “EMPTYPE”. (3 marks)
(ii) Create a pie chart based on the query in c(i) above to display the proportions of employees in various job descriptions. Save the report as CHART. (3 marks)
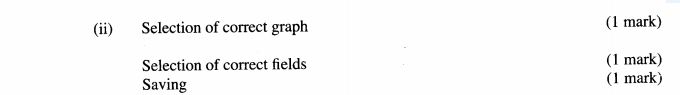
(d) Print the:
(i) three tables:
(ii) two reports;
(iii) output of query results for EMPTYPE. (3 marks)
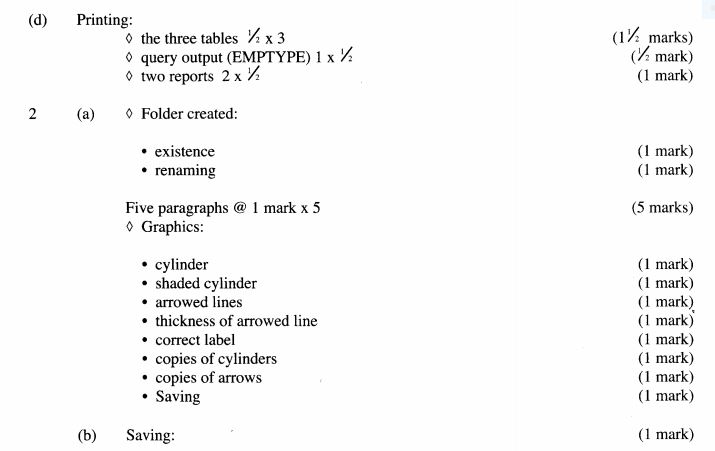
2 (a) Create a folder. The name of the folder should be the last three digits of your index number. Type the document below exactly as it appears using a word processing package and save it as LANGUAGE in the folder created. (15 marks)
DATABASE LANGUAGES
in the early years of database usage, they were accessed by writing programs in a high level procedural language such as COBOL. This required the skills of an experienced programmer who had a thorough knowledge of database design as well as familiarity with a language. As a result. access to databases was limited to those with procedural language skills. .
Modern databases can be accessed through easy-to-use query languages. Query languages are similar to English and require little programming knowledge. Commands entered through a computer terminal direct the machine to:
Search files
Make comparison
Generate reports
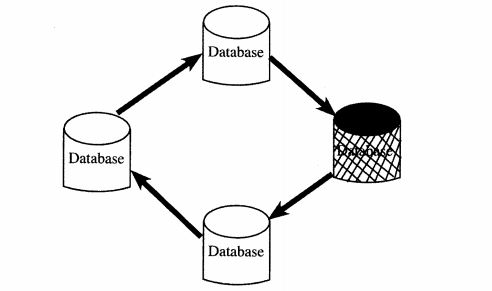
The utility of databases has greatly expanded because of query languages, even the users can easily access complex databases, searching out specific pieces of data and generating reports quickly and easily. Databases can be configured as follows; as single user database, multi-user database and as distributed database.
For example, a distributed configuration structure is shown below:
(b) Save a copy of the document created above as “FINAL LANGUAGE” in the folder created in (a) above and use it to answer parts (c) and (d). (1 mark)
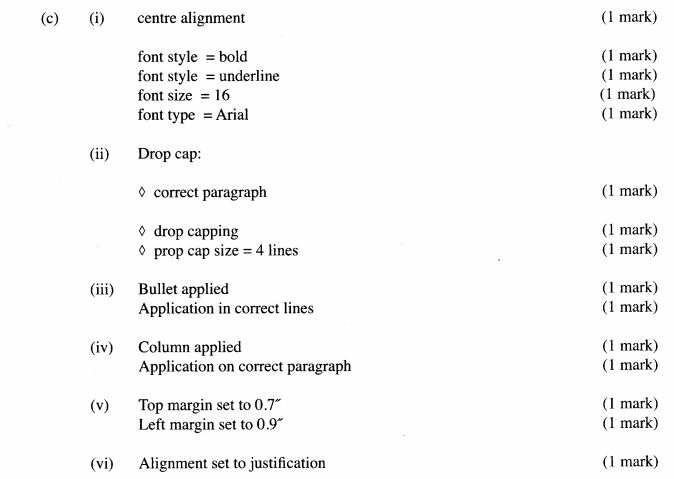
(c) (i) Format the heading “DATABASE LANGUAGES” as follows: (5 marks)
Alignment: Center
Font style: Bold and underline
Font size: 16
Font type: Arial
(ii) Drop the first letter of the paragraph starting with the word “Modem” by four lines. (3 marks)
(iii) Apply bullets to the list starting with the statement “Search files”, (2 marks)
(iv) Convert the paragraph starting with “The utility of…” to two columns. (2 marks)
(v) Set the page margins as follows:
(I) Top = 0.7” (t.78)cm
(II) Left = 0.9”(2.29cm) (2 marks)
(vi) Set the paragraph staxting with “In the early…” such that the text is evenly aligned along both left and right margins. (1 mark)
(vii) Correct the spelling errors. (1 mark)
(viii) Set the line spacing of the paragraph starting with the word “The utility…” to 1.5. (2 marks)
(ix) Move the first paragraph to come after the drawing. (2 marks)
(x) insert the following in the footer: (4 marks)
~ A line of length 6” (15.24cm) long.
~ Your name and index number,
(d) (i) Create a table at the end of the document created in (b) above and enter the following data: (3 marks)
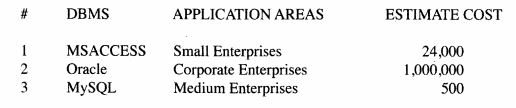
(ii) Enter the heading “EXAMPLES OF DATABASES” as the entire first row of the table. (3 marks)
(iii) Use a formula to find the average estimate cost of the DBMS applications in the table.
(iv) Save the document. (2 marks)
(e) Print the documents; LANGUAGE and FINAL LANGUAGE. (2 marks)
2011 KCSE Computer Studies-Marking Scheme/Answers